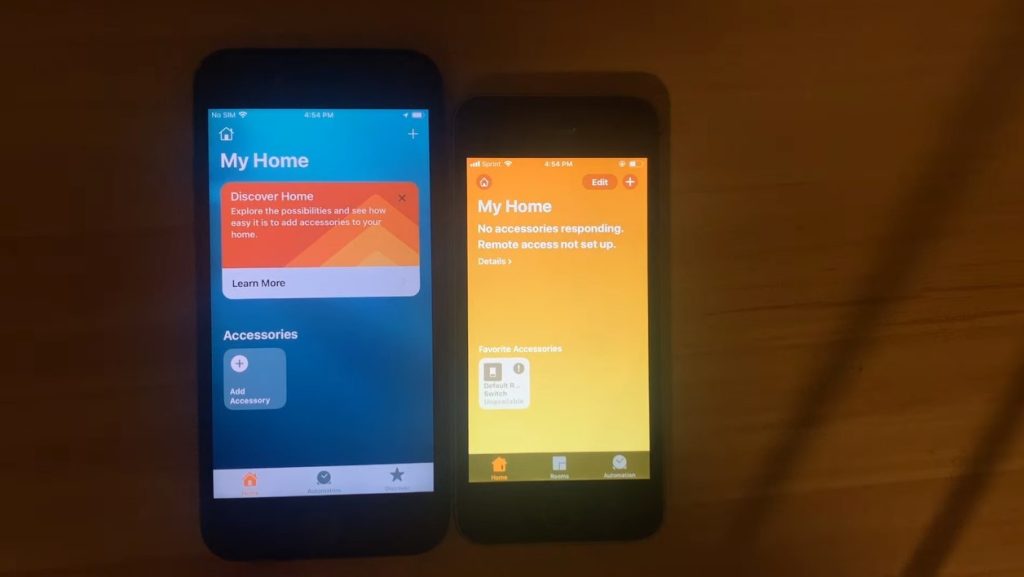
Security analyst Trevor Spinolas has revealed a flaw in Apple’s HomeKit home automation software, which allows it to trigger service denials on any device running iOS, including version 15.2. There was an error managing the names of the products connected to the HomeKit network. If any of these names are too long (over 500,000 characters, for example), any iOS device that connects to that network will crash, as you can see in this video.
https://www.youtube.com/watch?v=_BmI5Otsm9I
Often the attack scene is when a hacker creates such a homekit network and then invites someone to join. If the person accepts, the device will download data from that homekit network via iCloud, and then the operating system will be disabled. The only way out of this mess is to recover the device without logging in to iCloud. When the device reboots, you can connect to iCloud until access to HomeKit is immediately disabled to avoid downloading malicious data.
Obviously, this solution is not very satisfactory because we lose HomeKit functionality. Those with Xcode development skills can go one step further and use the exploit code posted by Trevor Spiniolas on GitHub to rename all the malicious content in the HomeKit network. Unfortunately, there is no easy way to fix the problem.
Find out more in the video:
On August 10, 2021, Apple warned of this problem. The company said it would provide the solution “early in 2022”, but the researcher hopes to address this shortcoming. “I think this bug allows ransomware to build on iOS, which is incredibly important”, He points out in a blog post. In view of this risk, Mr Spinolas felt that it would be better to inform the public now, rather than waiting for the release of the patch.
Proof: Blog note

Professional bacon fanatic. Explorer. Avid pop culture expert. Introvert. Amateur web evangelist.










More Stories
Acrylic Nails for the Modern Professional: Balancing Style and Practicality
The Majestic Journey of the African Spurred Tortoise: A Guide to Care and Habitat
Choosing Between a Russian and a Greek Tortoise: What You Need to Know