Dangerous applications are on the rise, just like the Google Play Store is always alert and removes everything that doesn’t work, new dangers are always lurking. However, it is The Joker This is one of the utility-level threats that causes a lot of damage and it uses many techniques to do this. So anything is possible from software changes to downloading threats after installing applications. These are specifically designed to steal messages. Short messageAnd Contact listEven the registration of victims in device information and value-added services.
WARNING! Check out these 11 dangerous apps on the Google Play Store!
Security Institutional Committee Zscaler The Joker constantly monitors malware, thus detecting multiple downloads on the Play Store. Threatlobes immediately notified the Google team that malicious applications were now being signed up quickly.
In fact, they were the most dangerous applications and various programs were able to escape from the control of Google.
The infected apps found in the Google Play Store are:
- Free soft news
- PDF Image Scanner
- Deluxe keyboard
- Compatible with QR scanner
- PDF Converter Scanner
- Font style keyboard
- Free translation
- Tell the news
- Special news
- Read the scanner
- Print scanner
Some types of applications are more vulnerable than others
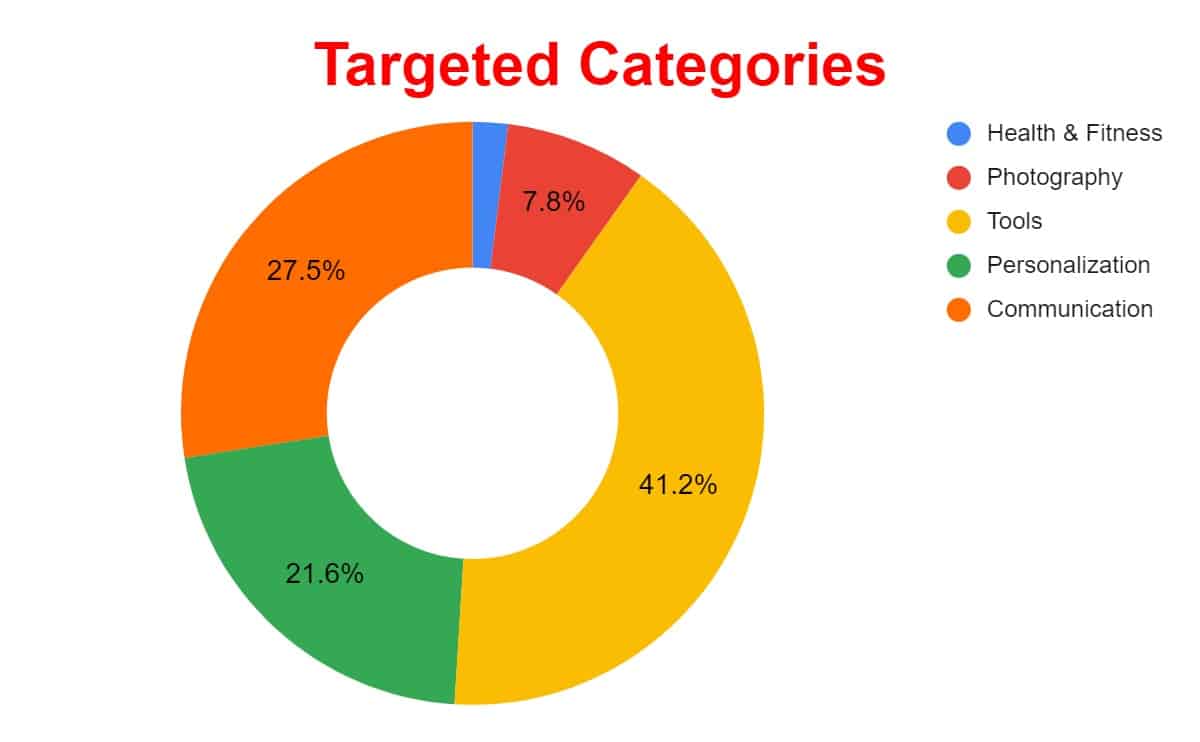
If you look at the most vulnerable applications, you can see that there are five categories that are most vulnerable to attack. Making more downloads can be even more interesting.
However, we do have applications for health, photography, gadgets, personalization and communication. This means that even the most threatened type within these tools is taken into account. This is because people are usually looking for applications that can solve problems on smartphones.
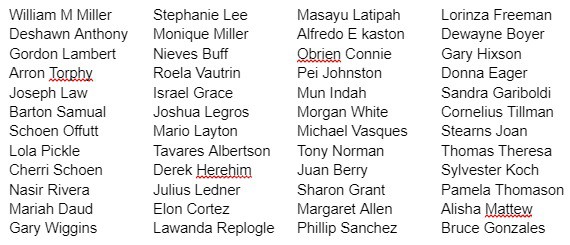
However, this security company did more than just report the affected apps. But he also revealed the names of the programmers responsible for it.
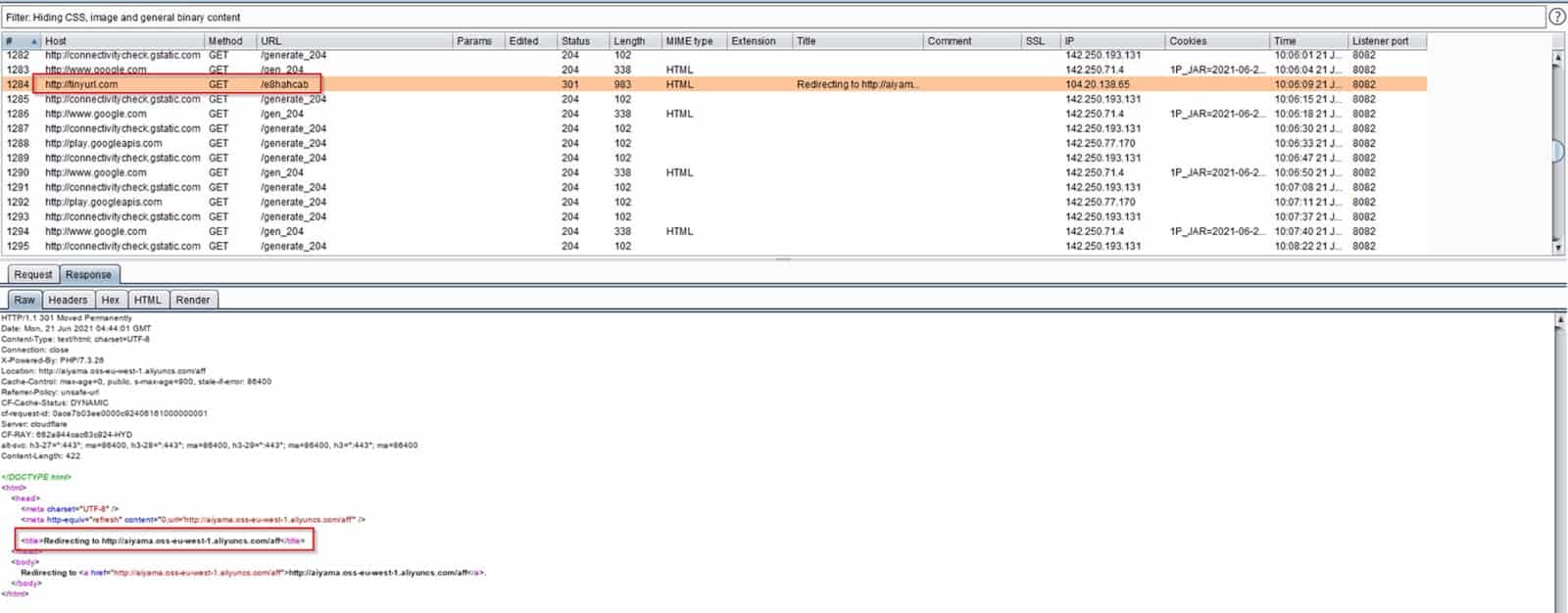
Address abbreviation services are a new method used by dangerous application developers.
What has happened so far is that malicious applications have downloaded malware through the standard connection to the Alibaba cloud. Use now URL shorten, From services such as in this case Small urlAnd bit.lyOr Rebrand.ly or zws.im or 27url.cn. It is difficult to identify threats.
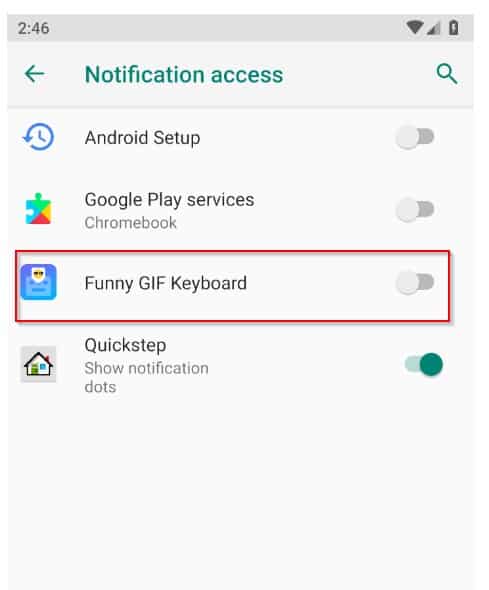
Abuse reporting system
The notification system is misused when these new threats are detected. After installing the applications, request access to this system as shown in the image below.
Once dangerous applications enter this computer, they can do whatever they want.

“Avid writer. Subtly charming alcohol fanatic. Total twitter junkie. Coffee enthusiast. Proud gamer. Web aficionado. Music advocate. Zombie lover. Reader.”










More Stories
What Does the Future of Gaming Look Like?
Throne and Liberty – First Impression Overview
Ethereum Use Cases