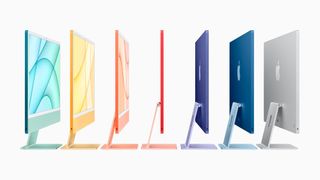
Data security gap in Apple file partition Apple does not just share Air Drop files
Author: Christine Reinterner
With Air Drop, Apple users can share files with each other. Studies by TU Tormstad show that even the uninvited can access the data. Apple has not yet closed the discovered data security gap. This is how an unsafe air drop can be replaced.
Company in this case
(Image: John Alexander / Pixabe)
Snapshots, presentations, videos – iPhones and MacBook users can easily share such files with each other. This is made possible by the Air Drop functionality, which allows files to be sent directly from one Apple device to another.
Since secret files are usually sent only to known individuals, AirDrop only shows the recipient devices of the address book contacts by default. To determine if the other party is a contact, AirDrop uses an authentication method that compares its own contact data with the entries in the other device’s address book.
Researchers at the Secure Mobile Networking Laboratory (SEEMOO) and the Cryptography and Privacy Engineering Team (ENCRYPTO) at TU Dormstad have examined this process very closely and identified a serious data security problem.
Attackers can intercept Apple users’ phone numbers and email addresses – without any prior knowledge of their victims. The attack requires only physical proximity to those with a WiFi enabled device and Apple devices. Once a person opens the ‘Share’ menu, the detection process starts on the Apple device and the attacker can “hook up”.
Discovered data security gaps can be found in so-called hash functions, which Apple uses to “hide” contact data during authentication. However, researchers at TU Tormstad have already proven that exchanging hash phone numbers is unsafe because they can be quickly counted, for example, by rogue attacks.
The new cryptographic protocol guarantees data security
Christian Weinert and the research team around Dr.-Ing. Milan Stud has also developed a workable solution that can replace an unsafe air drop. Private Drop is based on cryptographic algorithms for ‘private set intersection’, i.e. for the secure calculation of the intersection of confidential data sets.
With this method, mutual authentication can be carried out without exchanging vulnerable hash values. Private Drop was implemented by researchers on Apple devices for testing purposes. Measurements show that performance can compete with an insecure air drop: the time required for authentication is less than a second.
Researchers reported the discovery to Apple in early May 2019. So far, Apple has not confirmed the data security gap or announced that it will work on a solution, making more than 1.5 billion Apple device users vulnerable. The only way to protect yourself at this time is to disable Air Drop Detection on system settings and do not open the ‘Share’ menu.
The results of the research were published in a scientific article presented at the USInix Defense Symposium in August.
Original release:
(ID: 47365812)

“Avid writer. Subtly charming alcohol fanatic. Total twitter junkie. Coffee enthusiast. Proud gamer. Web aficionado. Music advocate. Zombie lover. Reader.”










More Stories
What Does the Future of Gaming Look Like?
Throne and Liberty – First Impression Overview
Ethereum Use Cases